Executive Summary
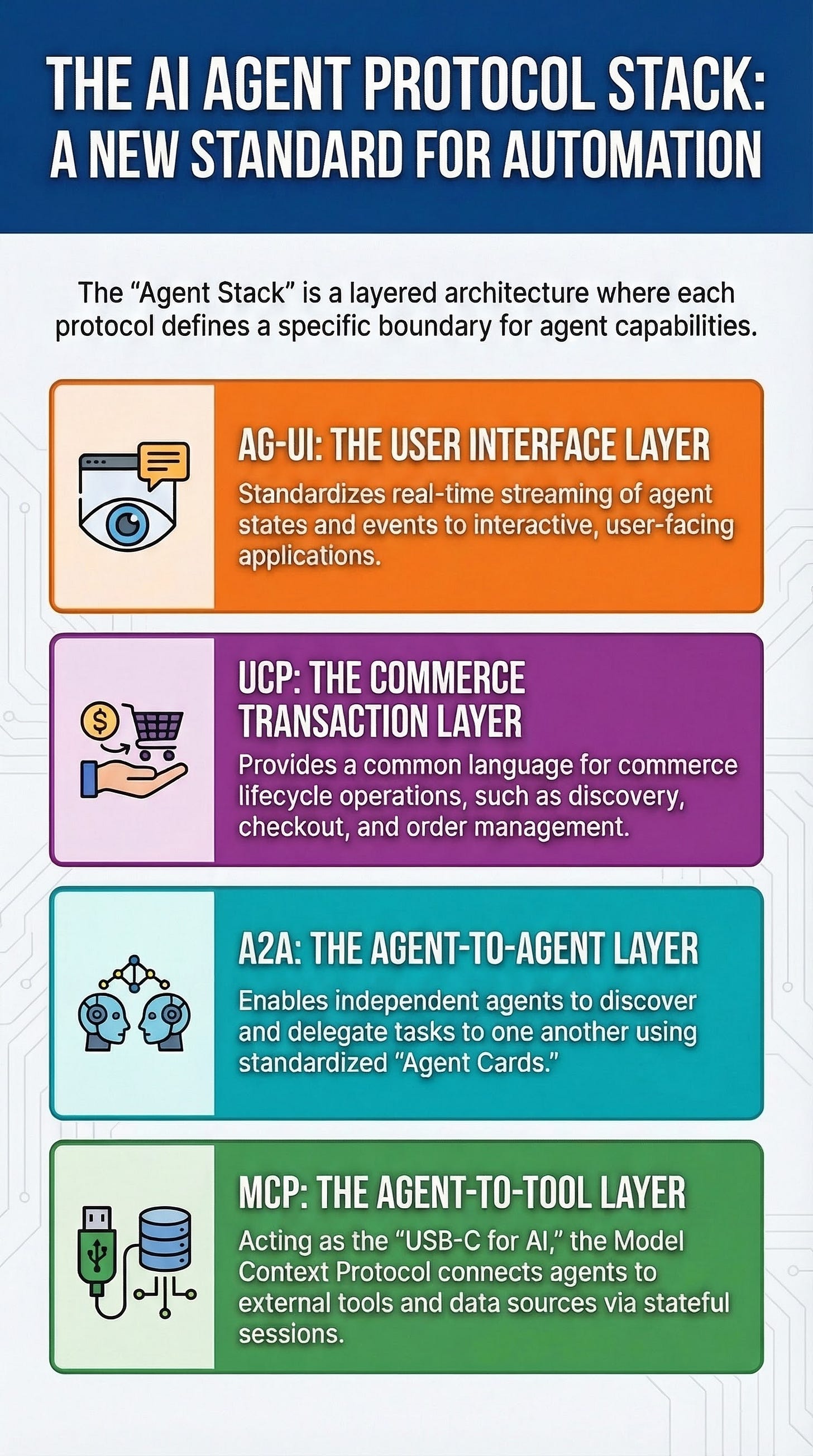
As of March 2026, the AI agent ecosystem has transitioned from fragmented, competing standards to a structured, layered “stack” architecture. This evolution, often compared to the “TCP/IP moment” for networking, is characterized by the complementary use of specific protocols to solve distinct agentic challenges: tool integration (MCP), agent-to-agent delegation (A2A), and commerce lifecycle management (UCP).
Critical takeaways from the current research and development landscape include:
The Layered Composition Model: Modern agent architecture now utilizes a specialized stack where MCP connects agents to data, A2A enables inter-agent collaboration, UCP standardizes commerce, and AG-UI manages real-time user interaction.
Protocol Maturity: The release of A2A v1.0 on March 12, 2026, and Google’s “Developer’s Guide to AI Agent Protocols” on March 18, 2026, have solidified the framing of these protocols as a unified pipeline.
Production Realities: While the stack enables complex supply-chain automation—demonstrated by organizations like Tyson Foods and Gordon Food Service—challenges remain regarding token overhead, authentication friction, and the “truthiness” of self-declared agent capabilities.
Observability Requirements: Production deployment requires cross-protocol tracing via OpenTelemetry and Cloud Trace to manage different failure domains across protocol hops.
--------------------------------------------------------------------------------
The Agent Protocol Layer Map
The “Agent Protocol Stack” is defined by clear boundaries that determine which protocol is utilized based on the task requirement.
Protocol Taxonomy and Functional Boundaries
Protocol
Primary Layer
Core Function
Discovery Mechanism
AG-UI / A2UI
Application / Experience
Standardizes agent-to-user interaction and UI streaming.
N/A
A2A
Service / Coordination
Facilitates communication and task delegation between independent agents.
/.well-known/agent-card.json
MCP
Integration / Actions
Connects AI applications to external systems, tools, and data.
list_tools via JSON-RPC 2.0
UCP
Integration / Actions
Provides a common language for commerce (checkout, orders, catalog).
/.well-known/ucp
AP2
Security / Payment
Handles secure agentic payment authorization.
Integrated with UCP/A2A
--------------------------------------------------------------------------------
Deep Dive: Core Protocols of the Stack
1. Model Context Protocol (MCP)
Defined as the “USB-C for AI applications,” MCP is an open-source standard for connecting agents to tools and data sources.
Architecture: Based on JSON-RPC 2.0, supporting stateful connections and capability negotiation.
Primitives: Focuses on tools, resources, and prompts.
2026 Roadmap: Priorities have shifted toward stateless, horizontally scalable operation behind load balancers and the introduction of “Server Cards” via
.well-knownmetadata.Integration: The Agent Development Kit (ADK) uses
McpToolsetfor connection management and schema adaptation.
2. Agent2Agent Protocol (A2A)
A2A provides the interoperability layer for agents built by different organizations to communicate.
Governance: Originally developed by Google; now governed by The Linux Foundation.
Discovery: Servers must expose an Agent Card at a standardized URI. These cards may be signed with JWS for security, though signing remains optional.
Capability Differentiation: A2A supports “Extended Agent Cards” which are only accessible after authentication, allowing for context-specific capability disclosure.
3. Universal Commerce Protocol (UCP)
Launched in January 2026, UCP serves as the transaction layer, designed to integrate with existing retail infrastructure and Shopify-scale commerce systems.
Design Rationale: Avoids monolithic protocol collapse by using a layered approach: core transaction primitives, higher-level versioned capabilities (Orders, Catalog), and composable extensions.
Workflow: Agents discover merchant capabilities via a JSON manifest at
/.well-known/ucpbefore executing checkout or order management.
--------------------------------------------------------------------------------
Reference Architecture: The Supply-Chain Pipeline
A primary use case for the full protocol stack is the restaurant supply-chain agent, which decomposes complex workflows into three distinct agent roles.
Operational Sequence
Inventory Agent (MCP Boundary): Vertically integrates with local databases. It uses MCP tools to query real-time stock levels and identify reorder needs.
Procurement Agent (A2A Boundary): Handles horizontal delegation. The root orchestrator identifies this agent via its Agent Card and requests quotes or lead times through A2A tasks.
Commerce Agent (UCP Boundary): Interacts with external merchant boundaries. It discovers merchant profiles via UCP to execute purchase orders and secure payment via AP2.
Failure Domains and Recovery
Each “hop” in the pipeline represents a different trust and failure domain:
MCP Hop Failures: Tool unavailability or database latency. Recovery involves retries or falling back to read replicas.
A2A Hop Failures: Incompatible protocol bindings or “capability drift” (where an agent card claims skills the agent cannot currently perform). Recovery requires runtime validation and card verification.
UCP Hop Failures: Policy/identity requirements or payment authorization constraints. Recovery relies on capability discovery and versioned schema boundaries.
--------------------------------------------------------------------------------
Implementation and Observability
To make multi-protocol systems viable for production, developers must bridge the visibility gap between protocol handoffs.
Tracing and Telemetry
The Vertex AI Agent Engine supports OpenTelemetry for ADK agents. By enabling specific environment variables (e.g., GOOGLE_CLOUD_AGENT_ENGINE_ENABLE_TELEMETRY), developers can correlate traces across process and network boundaries. This allows for the creation of a “Protocol Boundary Timeline” that tracks:
Integration lines of code (LoC) per protocol.
Hop latency (p50/p95 metrics).
Token overhead for protocol discovery payloads.
The “Token Overhead” Critique
A significant point of industry debate concerns the context window cost of these protocols.
Critique: Figures such as Denis Yarats (Cofounder & CTO, Perplexity) have expressed concerns regarding MCP’s context window overhead and authentication friction.
Analysis: Cloudflare has argued that “directly exposing tools” can waste tokens because tool outputs must be re-ingested by the model. Their proposed “Code Mode” suggests reframing tool use as code generation to reduce round trips.
--------------------------------------------------------------------------------
Expert Nuance: Security and Capability Integrity
Agent Card “Truthiness”
The integrity of the A2A protocol depends heavily on the Agent Card, yet the current specification allows for “capability drift”—a mismatch between advertised and actual agent skills.
The Signing Gap: The A2A spec uses “MAY” and “SHOULD” language regarding digital signatures. Security analyses suggest that unsigned cards enable spoofing, as implementers may fail to treat cards as untrusted input.
Mitigation Strategy: Production-grade systems are encouraged to implement Heartbeat Capability Verification. This involves periodically running “conformance probe” tasks to verify that an agent’s output schema matches its Agent Card’s advertisements.
Graceful Degradation
Given the complexity of the stack, architectural resilience requires graceful degradation. If an A2A delegation fails due to an unexpected schema, the system should be designed to fall back to deterministic API paths or direct MCP tool calls for critical operations, ensuring the commerce lifecycle is not entirely disrupted by a single protocol failure.